Difference between TCP and UDP
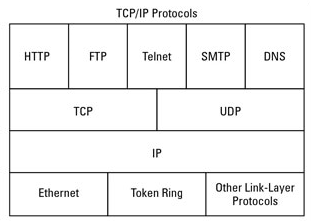
In networking, a protocol refers to a standardized method of performing specific tasks and organizing data to enable effective communication and comprehension between two or more devices. Various network protocols and standards are necessary to ensure seamless communication between computers, even if they are geographically distant from each other. Network protocol suites are typically organized into layers, following the OSI (Open Systems Interconnect) Reference Model designed by the International Standards Organization (ISO). This model comprises multiple layers that interact to facilitate data transmission and reception. Among these layers, the Internet Protocol (IP) plays a crucial role in the protocol hierarchy, ensuring the proper routing and delivery of data across interconnected networks.
Internet Protocol (IP)
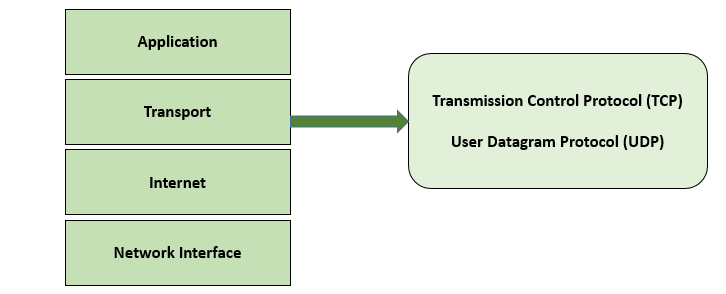
The Internet Protocol (IP) is a fundamental protocol responsible for routing and addressing data packets, ensuring their proper delivery across networks to their intended destinations. At the transport layer (Layer 4) of the TCP/IP protocol suite, two primary protocols exist: TCP (Transmission Control Protocol) and UDP (User Datagram Protocol). While TCP and UDP are not the only protocols operating on top of the Internet Protocol, they are the most commonly utilized ones. Both TCP and UDP are employed for transmitting data packets, referred to as packets, over the Internet. They rely on port (or socket) numbers to facilitate communication with higher layers of the protocol stack.
TCP
Transmission Control Protocol (TCP) stands as the preeminent protocol utilized across the Internet due to its remarkable error correction capabilities. TCP operates as a connection-oriented stream over an IP network, ensuring the precise and reliable delivery of data packets to their designated destinations in the correct sequence. This unparalleled reliability is largely attributed to the implementation of "flow control," a method that intelligently determines when data necessitates re-transmission and momentarily halts the data flow until previous packets have been successfully transferred. Consequently, this entails the utilization of acknowledgement packets sent back to the sender and automatic retransmission, albeit resulting in additional delays, and comparatively, a less optimally efficient transmission compared to the User Datagram Protocol (UDP).
Characteristics of TCP
- Connection-oriented.
- Reliable.
- Divides outgoing messages into segments.
- Reassembles messages at the destination station.
- Re-sends anything not received.
- Reassembles messages from incoming segments.
Examples of TCP in real life
- World Wide Web(HTTP)
- E-mail (SMTP TCP)
- File Transfer Protocol (FTP)
- Secure Shell (SSH)
UDP
The User Datagram Protocol (UDP) operates as a connection-less protocol, boasting faster data transmission compared to TCP but at the cost of reduced reliability. The guarantee of data integrity applies solely to individual datagrams, leading to the possibility of datagrams arriving out of order or not reaching their destination altogether. Unlike TCP, UDP sends packets directly to the target computer without establishing a prior connection, neglecting to indicate packet order or verify their successful delivery. Consequently, UDP finds limited use in scenarios where crucial data, such as webpages or database information, must be transmitted securely and accurately. Instead, it is more commonly employed for real-time communication, where a marginal percentage of packet loss is acceptable to avoid the overhead associated with TCP connections. Notably, UDP prioritizes speed over other considerations, hence impacting the quality of streaming media due to its propensity for potential packet loss.
Characteristics of UDP
- Connectionless.
- Unreliable.
- Transmit messages (called user datagrams).
- Provides no software checking for message delivery (unreliable).
- Does not reassemble incoming messages.
- Uses no acknowledgments.
- Provides no flow control.
Examples of UDP in real life
- Domain Name System (DNS)
- Streaming media applications such as movies
- Online multiplayer games
- Voice over IP (VoIP)
- Trivial File Transfer Protocol (TFTP)
Summary: TCP Vs. UDP
- TCP is connection oriented and reliable where as UDP is connection less and unreliable.
- TCP is heavy-weight, and UDP is lightweight.
- Header size is 20 bytes while UDP header size is 8 bytes.
- The speed for TCP is slower while the speed of UDP is faster.
- TCP uses handshake protocol like SYN, SYN-ACK, ACK while UDP uses no handshake protocols.
- TCP does error checking and also makes error recovery, on the other hand, UDP performs error checking, but it discards erroneous packets.
- TCP reads data as streams of bytes, and the message is transmitted to segment boundaries while UDP messages contain packets that were sent one by one. It also checks for integrity at the arrival time.
- What is the main difference between the C and C++ languages?
- What is the Difference between a Curriculum Vitae and a Resume
- What is the difference between weight and mass?
- Difference Between Alternating Current (AC) and Direct Current (DC)
- What are the differences between 1G, 2G, 3G, 4G and 5G?
- What's the difference between an Intel Core i3, i5 and i7?
- What is the Difference between Internet and Intranet
- Difference between compiler and interpreter
- What Is The Difference Between Data And Information
- What is the difference between IPv4 and IPv6
- What are the differences between hardware and software
- What is the Difference Between HTTP and HTTPS?
- Difference between Windows 10 Home and Windows 10 Pro
- What is the difference between LAN and WAN
- What Is the Difference Between a Router and a Modem?
- Difference Between 32-Bit and 64-Bit Operating Systems