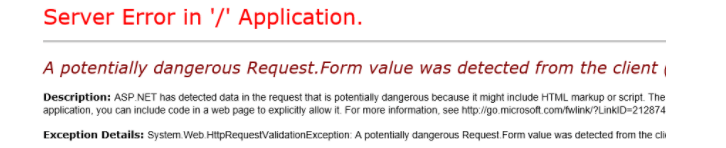
A potentially dangerous Request.Form value was detected from the client
The runtime raises an error when attempting to input HTML tags or content within a form. Although HTML tags themselves are not inherently harmful, their presence within certain contexts can pose a risk. This scenario could indicate a potential cross-site scripting (XSS) attack, which is why ASP.NET has a default restriction on allowing such input.
Filtering random input for dangerous characters is not a viable solution, as any character has the potential to be dangerous depending on the specific circumstances. It is crucial to implement appropriate security measures to mitigate the risks associated with HTML tags and prevent malicious attacks.
However, there may be instances where allowing users to post HTML tags is necessary. This could be due to a need for specific characters, such as "›", or to support the usage of tags like ‹h1› or ‹div› for certain development functionalities. In such cases, it is important to encode the input at the point where certain characters may become potentially dangerous by crossing into a different sub-language with special meanings.
How to solve?
To address this issue, you have two options. Firstly, you can HTML encode the input before submitting it, ensuring that any potentially harmful characters are appropriately encoded. Alternatively, you can disable request validation by setting ValidateRequest = false in the @Page directives within your .aspx file(s). However, it is crucial to note that disabling request validation can expose your site to Cross-Site Scripting (XSS) attacks, so caution must be exercised and appropriate security measures should be implemented to prevent any potential risks.
C# sample:The ValidateInput attribute can be utilized to selectively disable validation by ASP.NET MVC for a specific Action method within a Controller. By applying this attribute, the validation process will be bypassed for the designated Action method, allowing the inclusion of HTML content in the request.
Alternatively, you can use the [AllowHtml] attribute to annotate the specific property in your model that requires HTML. This attribute explicitly permits the inclusion of HTML markup during the model binding process, effectively bypassing request validation for that particular property.
The scope of the solution is limited to a specific property within the Model class, ensuring a targeted and secure approach.
For applications using .NET 4.0, it is important to include the following tag within the web.config file, specifically within the ‹system.web› tags:
Also, you can disable request validate entirely by specifying:
- Asp.Net Interview Questions (Part-1)
- Asp.Net Interview Questions (Part-2)
- Advantages of ASP.NET Web Development
- What is IIS - Internet Information Server
- What is Virtual Directory
- What is HttpHandler
- Page Directives in Asp.Net
- What is a postback
- What is IsPostBack
- What is global.asax
- Difference between Machine.config and web.config
- Difference between HTML control and Web Server control
- What is Query String
- Difference between Authentication and Authorization
- How to secure Connection Strings
- What is ASP.Net tracing
- Passing values between Asp.Net pages
- Differentiate between client side validation and server side validation
- How to Get host domain from URL
- Adding a Favicon To Your Website
- Asp.Net Textbox value in Javascript
- AutoEventWireup attribute in ASP.NET
- Can I use multiple programming languages in a ASP.net Web Application?
- Difference: Response.Write and Response.Output.Write
- How many web.config files can I have in an application?
- What is Protected Configuration in asp.net?
- Static variablesin .Net , what is their life span?
- Difference between ASP Session and ASP.NET Session?
- What does mean Stateless in Asp.Net?
- What is the Difference between session and caching?
- What are different types of caching using cache object of ASP.NET?
- Which method is used to remove the cache object?
- How many types of Cookies are available in ASP.NET?
- What is Page Life Cycle in ASP.net?
- What is the code behind and Inline Code in Asp.Net?
- What is master page in ASP.NET?
- Can you change a Master Page dynamically at runtime?
- What is cross-page posting in ASP.NET?
- How to redirect a page in asp.net without performing a round trip ?
- How to register custom server control on ASP.NET page?
- How do you validate Input data in Asp.Net?
- What's the difference between ViewData and ViewBag?
- Difference between Response.Redirect and Server.Transfer
- What is the function of the CustomValidator control?
- Define RequiredFieldValidator?
- Difference between custom control and user control
- Difference between Label and Literal control in ASP.Net
- What are the major events in Global.Asax file?
- What is Event Bubbling in asp.net ?
- What is Delay signing?
- What is the difference between in-proc and out-of-proc?
- What is the difference between POST and GET?